...
Access the Okta admin portal
Access the Application you setup for the LogiSense Billing integration
Click on the General link
Under the App Settings section click Edit
Check the option Enable SCIM provisioning
Click Save
Once the change is saved a new Provisioning link will appear under the application where SCIM settings can be populated
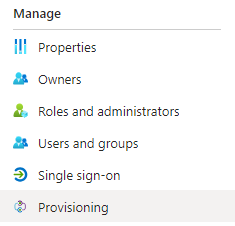
Click on Provisioning
On the Provisioning Settings page click Edit
In the SCIM connector base URL field enter the domain of your LogiSense Billing system followed by /ResourceServer/api/SCIM
In the Unique identifier field for users field enter your Okta supplied identifier
In the Supported provisioning actions section enable Push New Users, Push Profile Updates and Push Groups
Change the Authentication Mode to HTTP Header authentication
Under the HTTP Header section in the Bearer field paste the SCIM Access Token you copied earlier from the SAML Settings in the LogiSense Billing application
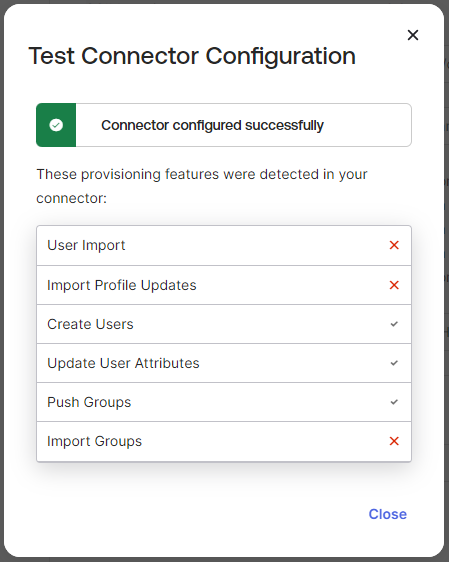
Click Test Connector Configuration
On the pop-up that appears the test should show that the testing of the create, update and push functions worked
Close the Test Connector Configuration pop-up and Click Save
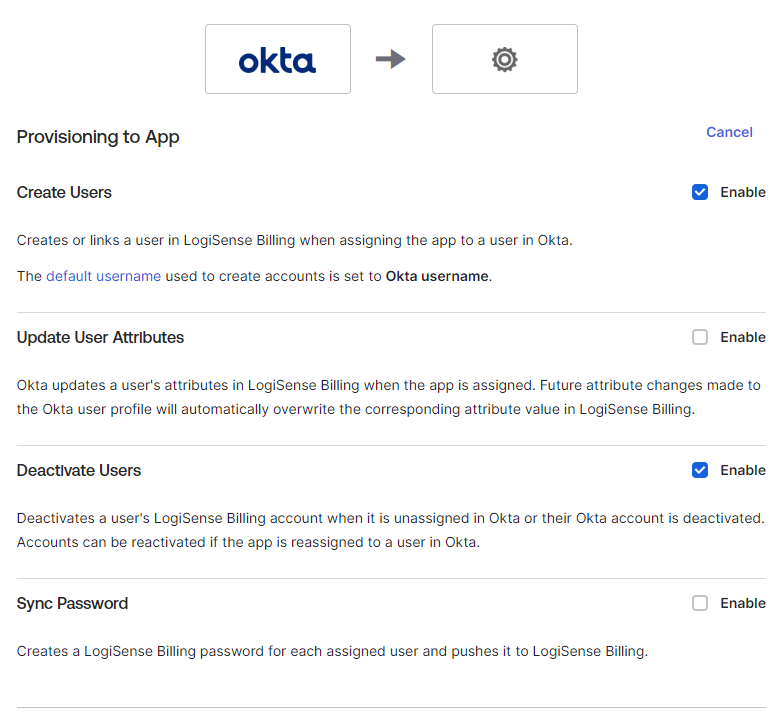
Next, we need to grant Okta user management permissions in LogiSense Billing. On the Provisioning page click the Edit link
Next to Create Users click Enable
Next to Deactivate Users click Enable
Click Save
Configure a SCIM Role Group in LogiSense Billing (Optional)
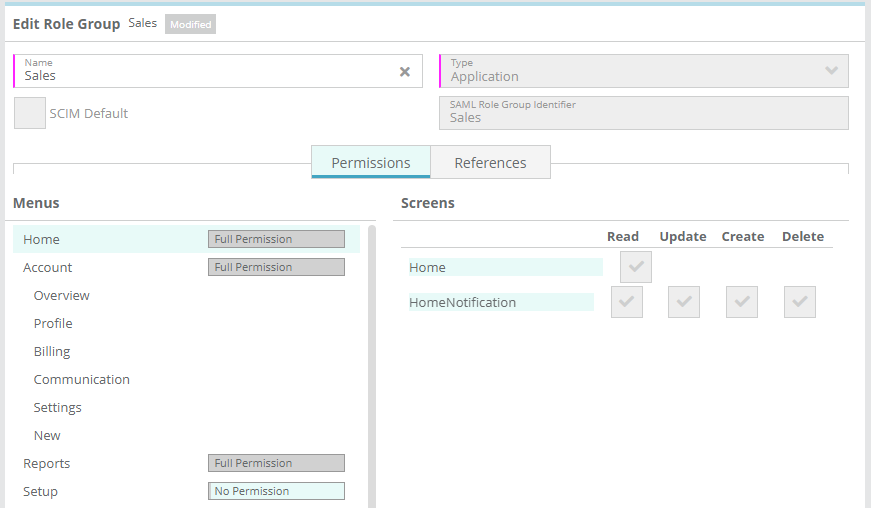
When people are assigned to the Application in Okta they will be pushed (created) in LogiSense Billing as users. The role group that the user is assigned to determine their permissions is the ‘SCIM Default’ role group (shown below)If the person in Okta has no group set on it then the user will be created using the role group setup as the ‘SCIM Default’ in LogiSense Billing.
...
The preconfigured SCIM Default role group in LogiSense Billing is the ‘ReadOnly’ role group. This is a core role group that grants the user read only access to all menus and screens but no rights to modify anything. SCIM users in LogiSense billing cannot have role groups deleted from their roles, so if you wish to restrict what menus and screens SCIM users can see you will need to
If you wish to grant Okta users without groups different permissions in LogiSense billing (e.g. more limited access such as read only access to the home screen) you can create a new role group set in LogiSense Billing with the SCIM Default option set. This The new role group can be setup with minimum permissions (e.g. read only access to the home screen) and then additional role groups can be assigned to the user to impart additional rights (e.g. an accounting role group can be added to the user granting read/edit access to accounts and reports)will then be the new default role group for all Okta people pushed to LogiSense Billing going forward.
Groups setup in Okta and pushed will create SCIM role groups in LogiSense Billing, so there is no need to setup additional role groups beyond the SCIM Default role group in LogiSense Billing. Instructions on how to push groups from Okta to LogiSense Billing are covered below in this guide.
...
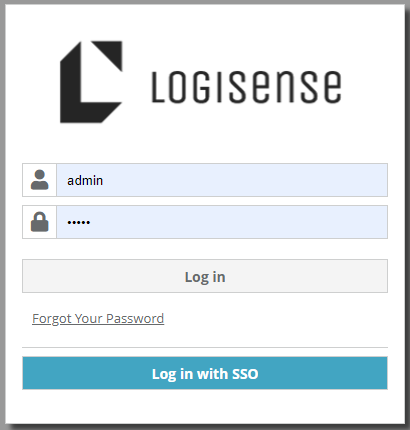
Log out of LogiSense Billing
On the Login page a new Log in with SSO option will be available
Click on Log in with SSO
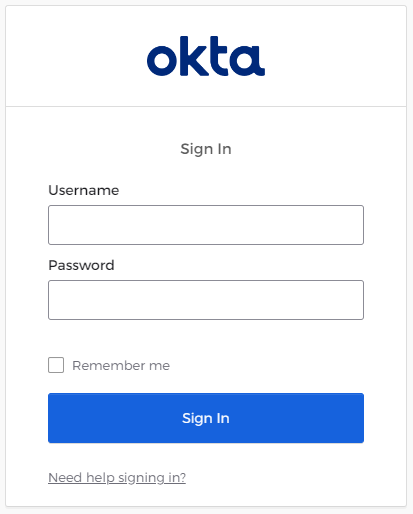
You will be redirected to the Okta login page
Enter your Okta username and password and click Sign In
After entering valid login Okta credentials you will be directed to the LogiSense Billing application and logged in
The signed in user will now be able to view/modify all of the screens in LogiSense Billing that their role group configuration permits them to access.
...
Login to LogiSense Billing
Load the Setup / Users & Accounts / Owners screen
Under Owner Configuration click on SAML Setting
Click Enabled if it is not already selected
In the Entity ID field paste in the Azure AD Identifier you copied during the Application setup process
In the Provider Metadata URL field paste in the Azure APP Federation ID you copied during the Application setup process
Click the Get Token button and a token will be generated
Copy the SCIM Access Token that is generated (this will be needed as part of the SCIM Configuration below)
Click Save to save the SAML settings
Configure a SCIM Role Group in LogiSense Billing (Optional)
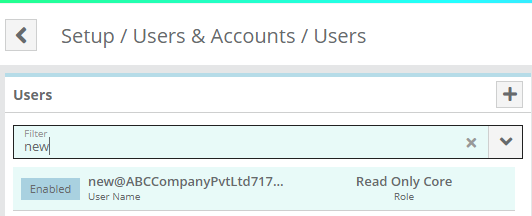
When users are provisioned to the Application in Azure AD they will be pushed (created) in LogiSense Billing as users. The role group that the user is assigned to determine their permissions is the ‘SCIM Default’ role group (shown below)If the user in Azure has no group set on it then the user will be created using the role group setup as the ‘SCIM Default’ in LogiSense Billing.
...
The preconfigured SCIM Default role group in LogiSense Billing is the ‘ReadOnly’ role group. This is a core role group that grants the user read only access to all menus and screens but no rights to modify anything. SCIM users in LogiSense billing cannot have role groups deleted from their roles, so if you wish to restrict what menus and screens SCIM users can see you will need to
If you wish to grant Azure users without groups different permissions in LogiSense billing (e.g. more limited access such as read only access to the home screen) you can create a new role group set in LogiSense Billing with the SCIM Default option set. This The new role group can be setup with minimum permissions (e.g. read only access to the home screen) and then additional role groups can be assigned to the user to impart additional rights (e.g. an accounting role group can be added to the user granting read/edit access to accounts and reports)will then be the new default role group for all Azure users pushed to LogiSense Billing going forward.
Groups setup in Azure AD and pushed will create SCIM role groups in LogiSense Billing, so there is no need to setup additional role groups beyond the SCIM Default role group in LogiSense Billing. Instructions on how to push groups from Azure AD to LogiSense Billing are covered below in this guide.
...
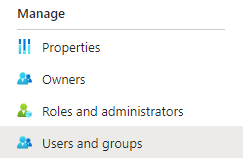
Access the Azure portal and load your application
Click on Users and Groups on the left sidebar
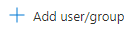
Click on Add user/group
Search/select and assign an existing Azure AD user if you haven’t already added a user or test user
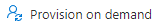
To test the integration provisioning the user. Access the
To test, you can force an update through the Provision On Demand tab. Access the Provisioning page using the left sidebar
Click on Provision on demand
Search for the user you wish to provision and click the Provision button
The Azure portal should display no errors and LogiSense Billing should display the new user that has been pushed to it
In the Azure portal you can follow the same process to provision additional users and groups as needed. Once these entities are created in LogiSense Billing you can configure the permissions for the role groups that you have pushed in order to define what Azure users in those groups can do in the LogiSense Billing application
Login to Test SSO Integration
Log out of LogiSense Billing
On the Login page a new Log in with SSO option will be available
Click on Log in with SSO
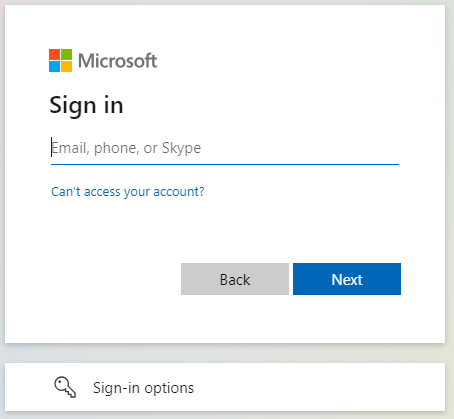
You will be redirected to the Azure login page
Enter your Azure AD email and password and click Sign In
After entering valid login credentials, you will be directed to the LogiSense Billing application and logged in
The signed in user will now be able to view/modify all of the screens in LogiSense Billing that their role group configuration permits them to access.